The Cyber Threat Assessment Program
There are exactly two ways to test your network’s security against cyber threats: run validation testing to assess precisely how your network performs or wait for the real thing to happen and draw conclusions while you’re picking up the pieces in the aftermath. While trial-by-fire is certainly a conclusive way to assess your network security, Firewalls.com strongly recommends the former option. Fortinet’s Cyber Threat Assessment Program is a convenient and non-intrusive process that lets you see where your network stands without interrupting day-to-day operations.
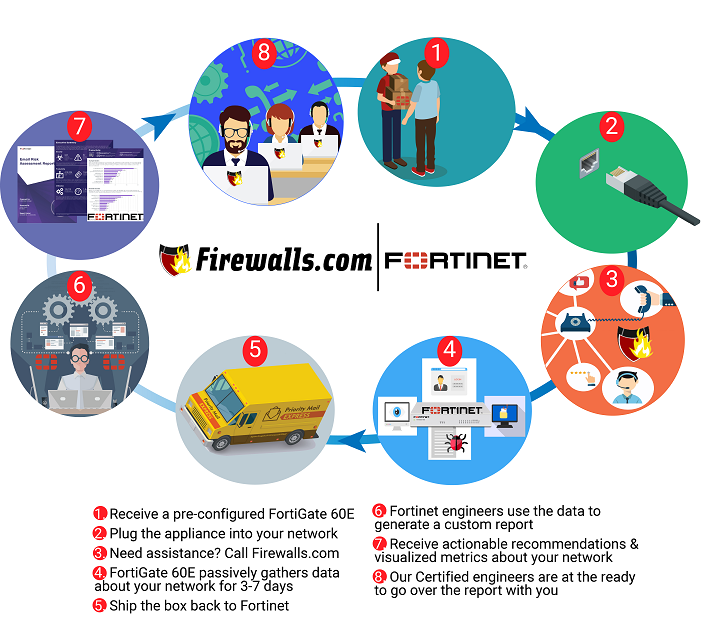
The assessment is free of charge, requires little to no legwork on your part, and yields results in just over a week. Check out the infographic below to see how it works, or listen to our recent podcast episode where we discuss Cyber Threat Assessments with Fortinet’s Ben Bolen.
See How Fortinet’s Secure SD-WAN Can Save You Time & Money
Been curious about SD-WAN? The very same process described in the infographic above can be used for an SD-WAN assessment as well! Fortinet’s Secure SD-WAN allows for high-speed application performance at the WAN edge, intelligently determining the ideal routes for MPLS, 3G/4G, or broadband traffic. Since traditional WAN architectures are not equipped to accommodate the high-demand workloads modern organizations who may be using applications spanning multiple cloud environments. Now you’re one FREE assessment away from seeing exactly how Secure SD-WAN can transform your network.
What Information Is Included In CTAP Report?
The Fortinet Cyber Threat Assessment focuses on three key areas: Security, User Productivity, & Network Utilization.
- Security: Details network vulnerabilities and helps to identify which devices and applications are at an elevated risk so that they can be properly secured. In this section of the report you’ll get to see which vulnerabilities and threats were observed bypassing your existing security solutions.
- User Productivity: Provides extensive visibility into peer-to-peer, messaging, and other application usage to see how users are using your network in their daily work. In this section you’ll see how spam, newsletters, and other cyber nuisances impact how your users navigate the network.
- Utilization: Provides real-world numbers about throughput and bandwidth usage during peak traffic. In this section, you’ll get to see when your network resources are needed most and where waste can be eliminated.
No Risk, No Extra Work, No Commitments
The infographic above outlines the basic process for receiving, setting up, and reviewing your results. At no point in the process are you required to make any purchases, change any settings, or meet any deadlines. Fortinet’s Cyber Threat Assessment is a risk-free program that requires no more extra work than plugging in a cord. If at any point you decide you want to end the test, pull the cord back out! That’s it. No money changes hands, no contracts are signed, and no network settings are changed. If you want to dump your final assessment in the trash, no problem. The report is yours to use as you see fit.
Ready For Your Free Assessment?
Getting your Cyber Threat Assessment is as easy as filling out a form on our Fortinet Cyber Threat Assessment Program page. Leave us your contact info and Firewalls.com will work behind the scenes to get a test set up for you. We work closely with Fortinet to make sure the test requires as little effort on your part is possible.