Detect third-party threats with real-time IT security alerts and structured response workflows to strengthen your business network.


Detect third-party threats with real-time IT security alerts and structured response workflows to strengthen your business network.

Choose the right port mode for your SonicWall Gen 8 firewall, comparing routing, transparent, tap, and advanced modes for improved security.
Managed firewall providers vs break-fix support explained. Compare proactive vs reactive security measures for your business.
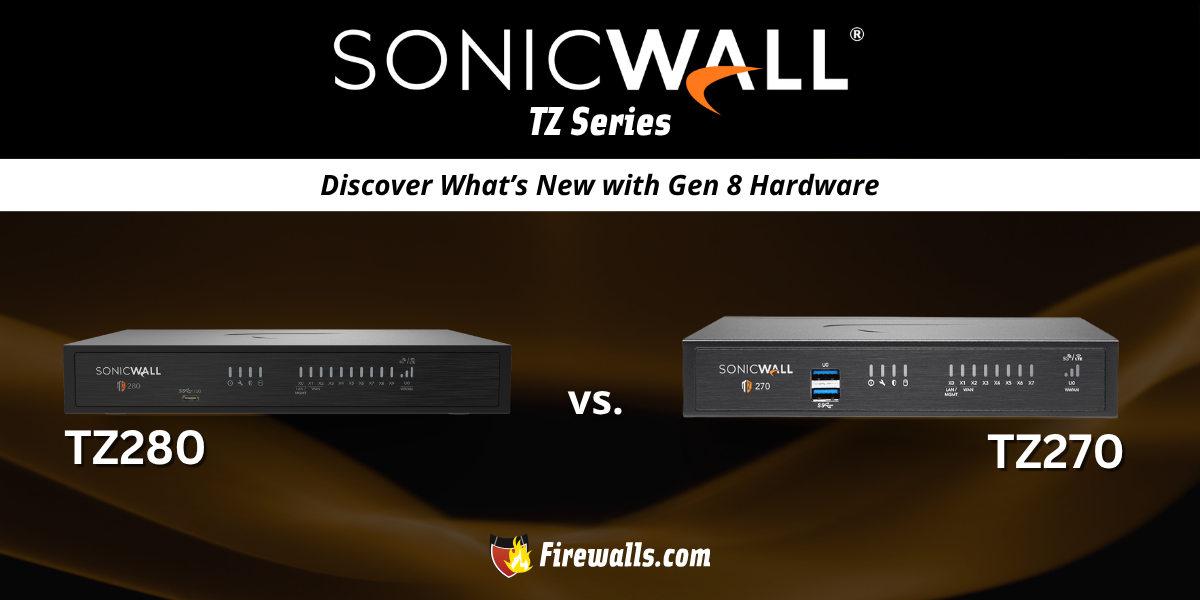
Compare specs performance between SonicWall TZ 280 vs TZ 270 for a better direction on choosing the best firewall for your business.

Firewall hardware lifecycle management covers multiple angles to ensure compliant, high-performance network protection.
Learn how Meraki vs SonicWall models TZ480 and MX250 stack up in throughput, security, and alignment for your business network.
Learn about firewall rules best practices for segmentation, logging, default deny policy, audits, and more to strengthen your network.

This Sophos vs Fortinet comparison lets you size up the XGS 4500 and FG-400F, while focusing on the unique specifications and security features involved.

Managed network monitoring delivers proactive security, 24/7 protection, and scalable oversight without the cost of in-house IT staff.

Explore the top rated data center firewalls for modern enterprise security, including options from SonicWall, Fortinet, and Cisco Meraki.