Firewalls.com Ultimate Fortinet Fortigate Buyers Guide
Our Ultimate Fortinet FortiGate Buyers Guide was designed to help small business owners, IT consultants, and network administrators understand the FortiGate catalog so that buyers are confident in their network security decision. Firewalls.com is committed to sharing plain-language product knowledge to our customers and partners.
Questions? Call toll-free at 317-225-4117 or email us at sales@firewalls.com.
FORTIGATE NEXT GENERATION FIREWALL
Fortinet FortiGate Firewalls are Secure SD-WAN-ready security platforms designed to protect home offices, SMBs, mid-sized, distributed enterprises, and branches. Highly efficient security processors optimize network performance with deep visibility and security effectiveness that routinely wins praises and recommendations from third-party benchmark tests.
FortiGate firewalls are available in many sizes, so finding a Fortinet FortiGate that fits your needs is simple. Fortinet's most popular firewalls belong to the D Series, E Series, & F Series. F Series is the latest generation of FortiGate firewalls.
FORTIGATE SERIES RESOURCES

FINDING YOUR NEXT FORTIGATE FIREWALL
Recommended User Counts – The most important consideration when buying a Fortinet next-gen firewall is the number of users your network must support. User counts means more than just the number of employees in your organization. A user is defined as any desktop, laptop, printer, phone, tablet, or other Internet-connected device operating on your organization’s network.
For optimal security, get an accurate count of every user in your system. Firewalls.com recommends leaving extra room for additional users in case your business grows or if you need to accommodate guest users. This also ensures there’s plenty of bandwidth for resource-heavy applications.
Throughput Speeds – A firewall’s throughput is a measure of the volume of Internet traffic that can pass through the firewall at any one time, based on the processing power of the hardware. Throughput is measured in Mbps (megabits per second) and Gbps (gigabits per second). Fortinet datasheets list a variety of throughput statistics based on the types of security services, traffic, and protocols that the firewall is handling.
Max Firewall Throughput – Max Firewall Throughput is the highest throughput statistic you will see on any datasheet because it denotes the maximum possible processing speed of the hardware when no additional services are deployed. This is the “out of the box” speed and, for most usage cases, does not reflect how a firewall will perform in a real-world scenario.
SSL VPN Throughput – Secure Socket Layer (SSL) and Virtual Private Networks (VPN) refer to communication protocols that govern how information is encrypted and transmitted between a source and its destination. Utilizing SSL VPN tunnels is the most secure means for remote workers, outposts, and branch offices to access resources from the primary database. Because a VPN is a private connection, throughput speeds are dependent on the kinds of data being transferred as well as the performance potential of the gateway encrypting and decrypting the traffic that passes through it.
IMIX Throughput – IMIX, or Internet Mix, refers to simulated traffic passing through a firewall to emulate how the hardware would perform in a real-world environment. IMIX throughputs represent the performance a firewall was able to achieve while handling a variety of packet sizes and traffic patterns. Internet Mix profiles are based on real-world samples captured by a selection of Internet routers and security sensors. This statistic will closely reflect the actual performance you can expect on your network.
Firewalls.com Recommends:
Business data is most secure when utilizing advanced scanning functions like Deep Packet Inspection and dedicated secure VPN tunnels. Shopping for firewalls based on Full DPI Throughput and SSL VPN Throughput guarantees your organization has plenty of performance potential to accommodate advanced services. When in doubt, assume your network will perform at 50%-70% of the throughput speeds listed on datasheets, leaving ample space for your network to grow.
Site-to-Site VPN Tunnels – Site-to-site VPN tunnels allow fixed-location Local Area Networks (LANs) to extend secure conduits to the main office intranet. DPI-SSL is included standard with any current generation Fortinet FortiGate firewall. FortiGate datasheets outline the maximum number of tunnels that a firewall can accept from remote LANs. These system specification tables will also include the max number of IPSec VPN clients supported.
Form Factor – The form factor of an appliance is the size and shape of the hardware. Most firewalls will have either a desktop form factor or rackmount form factor. Desktop form factor indicates that the firewall is a compact appliance, small enough to comfortably sit atop a desktop, while rackmount form factor specifies that the appliance was designed to be secured in a standard 19-inch server rack. Rackmount-sized appliances will sometimes indicate how many rack units (RU) the device occupies.
Wireless Support – Some organizations prefer wireless firewall solutions in lieu of appliances that must be connected via Cat5E/Cat6 cabling. Wired networking solutions are generally considered more reliable and more stable, especially because signals are not influenced or impeding by other connections. Wired appliances are generally much faster with data transfer speeds constantly improving thanks to the introduction of Gigabit interfaces. Wireless solutions such as FortiWifi wireless firewalls, however, do carry the benefit of additional mobility and flexibility of deployment, being able to reach any location without the limitations of physical cables. Wireless environments can also be installed more easily as they require less equipment and planning.
Firewalls.com Recommends:
Before making your cybersecurity investment, take stock of all the physical attributes of your facilities. Are building materials conducive or unfavorable to wireless signal transmission? Are power outlets plentiful and easy to reach? Are there certain areas that should be off-limits for Internet connectivity? Physical security should be an important concern when laying out your network and may impact the final hardware details you select.
Learn More About Firewall Tech Specs
Saving Money with Fortinet
Fortinet bundles their best-selling solutions together in comprehensive bundles so that customers can save money. Offered in 1-year, 3-year, and 5-year terms, bundles are progressively discounted to shave dollars off your expenses when you plan for long-term security.
In almost all situations, buyers should be looking to bundle their firewall with additional services or support. Appliance only purchases are typically only advisable if the hardware is going to be added to an existing network and should never be used for primary firewall protection.
Unified Threat Protection – Unified Threat Protection bundles are a basic suite of FortiGuard security services designed to extend your security infrastructure past the baseline of traditional firewalling. This entails 24x7 FortiCare support, along with App Control, IPS, AMP, Web Filtering, and AntiSpam.
Enterprise Protection – Extend enterprise-grade protection to small and mid-sized businesses with the Enterprise Protection bundle which included everything found in the Unified Threat Protection option, plus additional FortiGuard services like Security Rating Services, Industrial Controls ideal for manufacturers, & services that detect unknown Internet of Things (IoT) devices.
LICENSING FORTIGATE WITH ADVANCED SECURITY
Fortinet offers a wide variety of security add-ons & upgrades to guarantee your business data is always safe. Offers may be either a one-time upgrade or a recurring subscription. Similar to bundled solutions, customers can save substantially by opting for 3-Year or 5-Year subscriptions. Below you will find brief overviews of the standalone services offered by Fortinet. All of these services are included in some or all of the bundles outlined above.
FortiGuard App Control Service - Quickly create policies to allow, deny, or restrict access to applications or categories of applications
FortiGuard IPS Service - Stop both known & zero-day attacks like malware that attempt to breach your network defenses
FortiGuard Advanced Malware Protection - Combine Fortinet’s AntiVirus service with FortSandbox Cloud for robust core protection
FortiGuard Web Filtering Service - Subscription-based managed web filtering solution that sorts billions of webpages & sites into categories to be allowed, restricted, or blocked
FortiGuard AntiSpam Service - Use both send IP reputation & known spam signature databases to detect & block a wide variety of spam emails
FortiGuard Security Rating Service - Provides real-time risk & vulnerability data to audit system configurations & processes for improved network operations
FortiGuard Industrial Service - Monitor & regulate common ICS/SCADA protocols for visibility & control
FortiGuard IoT Detection - Subscription service that allows detection of unknown IoT devices that would not be found via regular local Device Database (CIDB)
GETTING MORE OUT OF YOUR FORTINET FORTIGATE
Firewalls.com Standard & Advanced FortiGate Configurations – Just say no to the set-up wizard. It’s time to take the guesswork out of network security. Firewalls.com’s in-house team of certified and specialized network architects completes all configuration work at our Indianapolis Security Operation Center (SOC), where full-time administrators optimize your network performance and security. Our team will complete a comprehensive survey of your network needs and configure your appliance to get the most out of your investment. By the time your hardware is delivered, it is fully loaded with a personalized configuration for an intelligent plug-n-play experience.
The Firewalls.com team will set up VPN tunnels, access points, co-location lockdowns, remote access and VoIP, configure granular content filtering, integrate the active directory, and establish purpose-built firewall policies, along with much more. Our proprietary 99-step configuration methodology leaves no stone unturned when it comes to transforming your network into a cyber fortress.
Learn More About Firewalls.com Configurations
Firewalls.com Managed Security Service – For small businesses, maintaining a robust IT staff may be a challenge. Firewalls.com employs a team of dedicated Fortinet professionals that can monitor, report, and mitigate attacks on your network around the clock, allowing you to get back to doing what you do best: running your business. Stop worrying about firmware updates and network downtime. Our peace-of-mind security services ensure a rapid response to whatever the bad guys throw at you. MSS delivers unlimited personalized support, proactive firmware updates, configuration changes, alerts, proactive threat detection, Web-based activity reporting, and equipment repair/replace.
Firewalls.com Managed Security Service is a month-to-month subscription service with no long-term commitments. Your network receives quarterly health checks to ensure your firewall is constantly evolving to meet the challenges of the threat landscape.
Learn More About Firewalls.com Managed Security Services
Firewall Configuration Checklist – Ready to tackle a firewall configuration yourself? Grab a copy of the Firewalls.com Configuration Quick Start Checklist, outlining all of the settings and decisions you’ll need to make along the journey. This 17-page checklist covers everything from internally hosted application settings to DHCP, TCP/UDP ports, rule documentation and more.
Get the Firewall Configuration Checklist
FortiCare Support – Fortinet offers standalone support contracts to extend technical support, firmware updates, and an extended warrant for your FortiGate firewall. FortiCare support is delivered via email, telephone, or web-based portal so that help is always within arm’s reach.
Learn More About FortiCare Support
About Fortinet
Fortinet develops cybersecurity products and services that range from firewalls to endpoint protection to network switches, and far more. Fortinet routinely ranks high among independent validators and third-party benchmark tests, having been recommended over 9 times by Gartner Magic Quadrant for Unified Threat Management. Fortinet continues to grow deeper and deeper roots in the small business network security arena and continue to push the boundaries of SMB firewalling with their FortiGate F Series.
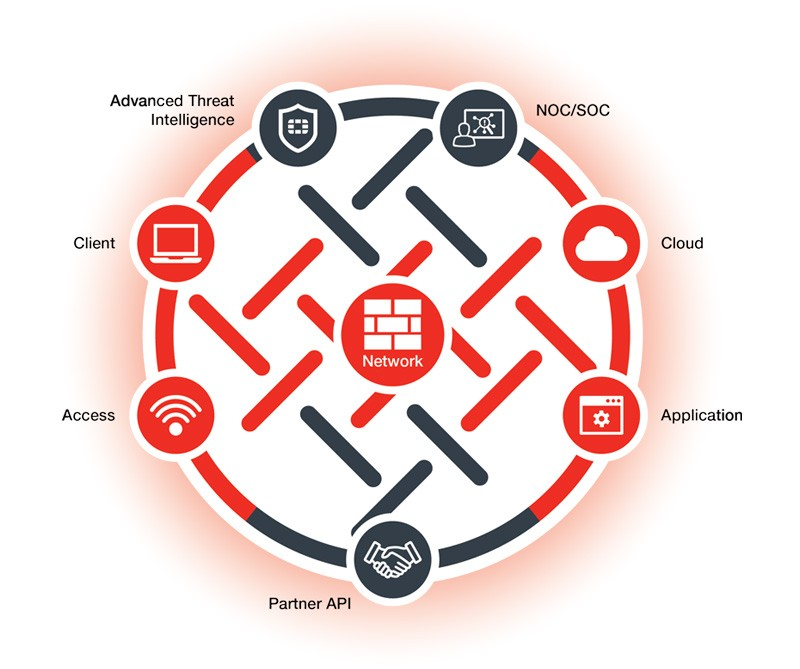
Fortinet Security Fabric – Fortinet boasts the real-time intelligence, detection capabilities, & integrated response in what they refer to as their “Security Fabric.” The Fortinet Security Fabric represents the holistic strategy of security-driven networking that ties together network access, cloud infrastructure, endpoint security, network edge, & application security. The Security Fabric provides complete end-to-end security, visibility, and control across your entire network infrastructure.
Learn More About Security Fabric Services
FortiGuard Labs Threat Intelligence - FortiGuard Labs represents the research and threat intelligence wing of Fortinet’s network security operations. By monitoring and anlyzing millions of threat signatures from around the globe, researchers at FortiGuard labs are able to get ahead of the attackers and release patches or new services to respond to changes in the threat landscape.
Learn More About FortiGuard
Why Choose Fortinet?
Why choose a FortiGate firewall? Don’t take our word for it. Below you’ll find just a handful of the industry awards lavished upon Fortinet’s products, services, and vision. We use words like "industry-leading" and "award-winning" when we talk about FortiGate Next Generation Firewalls, and below you'll find the proof in the pudding we're putting out.
- 2020 Frost & Sullivan - Network Security Provider Company of the Year in the Kingdom of Saudi Arabia
- Produkt Roku 2019 IT Professional : Fortinet FortiGate 500E readers’ choice
- 18th Star Nite Awards 2019
- 2019 MEF Awards
- 2019 Channel Awards - Best security Vendor category
- Network Innovation Awards
- HostingAdvice Developers’ Choice Award for FortiWeb Web Application Firewall
STILL NOT SOLD ON A FORTIGATE?
Let’s face it: cybersecurity is complicated. Firewalls.com encourages you to make an informed decision when purchasing any firewall because when the bad guys lose, we all win. Our account executives provide a low-pressure experience that’s heavy on product expertise and backed by decades of experience. Firewalls.com wants you to be 100% confident in your network security investment before any transactions begin.
I'm Ready to Buy a Fortinet FortiGateAlso check out the Firewalls.com Blog where you’ll find the latest Fortinet news, our Cyber Threat Dictionary, and product knowledge that equips you to take on the cyber threat landscape.