With dozens of competing firewall brands, each sporting several different models and variants in their product catalogs, it can be a serious challenge for non-experts (or even sometimes for experts) to navigate their options when purchasing a Next Generation Firewall appliance. Manufacturers do their best to be transparent about each firewall’s capabilities, but their datasheets often include 40 to 50 different metrics and measurements to sort through. Which hardware specifications are most important to a business network? What’s the difference between NGFW Throughput and SSL-VPN Throughput? Are maximum user counts really a hard limit? To get a clearer picture, we’ll dissect the tech specs of the FortiGate-60F to determine which stats matter most and why.
What on Earth are all of these numbers?!
Throughput Statistics
What is Firewall Throughput?
Maximum Firewall Throughput is the highest throughput speed stat in the tech specs and is measured in Mbps or Gbps – that’s megabits or gigabits per second. This statistic measures a firewall’s raw, unhindered processing speed in its base state–with no additional security services or processes activated. While knowing the maximum volume of traffic that can pass through your firewall is interesting, this stat does not usually provide a lot of context for how a product will behave on your real network. After all, nearly every firewall deployment will include some security services whether that’s antivirus scanning, intrusion prevention, or data loss prevention.
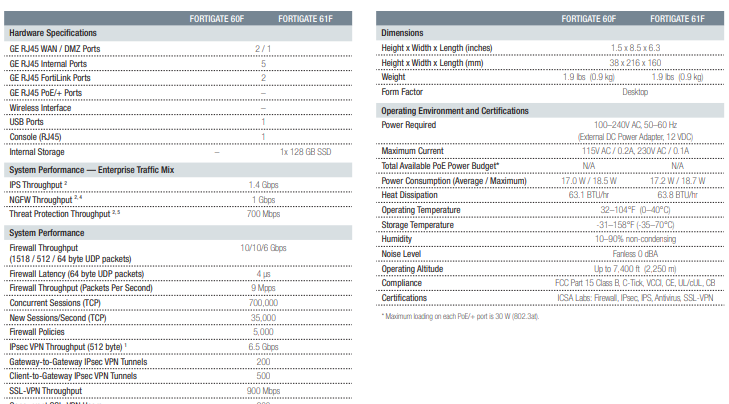
Note that the Firewall Throughput of the FortiGate-60F in this datasheet is written as 10/10/6 Gbps. These numbers demonstrate the maximum throughput of the firewall based on the size of data packets that makes up the traffic being scanned. While throughput is higher at 10 Gbps for larger 1518 byte UDP (user diagram protocol) packets, performance decreases when traffic is broken down into smaller, more numerous 64 byte packets. This is a process known as IP Fragmentation.
What is NGFW Throughput?
NGFW Throughput is a metric that you may not find in every manufacturer’s datasheets. In tables where you do find this statistic, it is generally a measure of throughput when Intrusion Prevention Services and Application Control (key next gen firewall services) are running. Because IPS and App Control are such common services, NGFW Throughput is a great statistic to indicate the speeds your appliance may exhibit in a real-world environment. The NGFW Throughput of the FortiGate-60F is a huge 1.0 Gbps, a major step up from its predecessor, the FortiGate-60E, which clocks in at 250 Mbps NGFW Throughput. That is a TON of speed for a small business firewall.
What is SSL-VPN Throughput?
SSL-VPN Throughput measures the volume of traffic that can pass through a firewall for a user who has connected to the network via an SSL-VPN (secure sockets layer virtual private network) remote access connection. Remote access solutions are exploding in popularity as more and more of the workforce becomes mobile. While the added productivity and freedom of a highly mobile workforce is a boon to modern business, it does call for additional layers of security to ensure that employees (and your data) stay safe no matter where they connect. SSL-VPN Throughput numbers tend to be much lower than other metrics because a lot of processing power is needed to decrypt, scan, and verify encrypted traffic. The SSL-VPN Throughput of the FG-60F is 900 Mbps, making it a great choice for remote branches and outposts.
SSL-VPN Throughput is especially crucial for any business that regularly allows users to work remotely. Depending on how much bandwidth is being called down by applications, low SSL-VPN Throughput can create bottlenecks for remote workers.
What is AntiVirus/AV-Proxy Throughput?
AV-Proxy Throughput is a statistic that some manufacturers are beginning to eliminate from their datasheets altogether. However, it can still be a helpful metric to understand. The stat measures the throughput available from a firewall when it is actively scanning traffic for viruses, malware, or other behavior patterns that indicate an attack. The reason this statistic is beginning to vanish from some datasheets is because traditional anti-virus scanning is evolving to more advanced behavior-based processes centered around Intrusion Prevention and deep packet inspection. Firewalls.com recommends basing your firewall decision on NGFW Throughput or SSL-VPN Throughput, depending on your individual network demands.
Fortinet datasheets have dropped the AV-Proxy statistic in favor of Threat Protection Throughput, which measures speeds for a firewall using IPS, Application Control, and Malware Protection with logging enabled. The Threat Protection Throughput of the FortiGate-60F is 700 Mbps.
Maximum Recommendations Statistics
What does Maximum Supported Access Points represent?
Simply put, this statistic tells you the maximum number of wireless access points that can be managed and secured by your firewall. This is a recommendation and not a hard limit. The “maximums” quoted in datasheets describe a rough number of access points that can be deployed on a network before they cause a large, negative impact on performance. Like many of the maximum recommended numbers in datasheets, these are guidelines to prevent you from overworking your firewall to the point of failure. The FortiGate-60F can easily support up to 30 FortiAPs.
How are Recommended User Counts measured?
Similar to the Maximum Supported Access Points section above, Recommended User Counts are a soft limit recommended by manufacturers to size an appliance for your network. Technically, you can allow any number of users to operate on any firewall, but past a certain point an appliance will slow to a crawl. To maintain comfortable performance speeds and bandwidth allocation, it’s best to stay within the bounds of recommended user ranges. The FortiGate-60F is intended for deployments of up to 25 users.
It is important to note that users are not simply the number of employees you expect to use your network. The term user in this case encompasses each Internet-connected device that may use the network on a daily basis. In network security, a user is considered any of the following:
- PCs, Laptops, & Workstations
- Mobile devices
- Internet of Things (IoT) devices
- Printers
- Tablets
- Any other device connected to the Internet
Firewalls.com recommends a firewall with roughly twice the capacity of users that you currently house on your network. This built-in wiggle room is so you can accommodate business growth and spikes in guest users, while still leaving plenty of processing power on the table for resource-intensive applications.
What does Maximum Concurrent Connections mean?
Maximum Concurrent Connections describes the total number of TCP (transmission control protocol) connections a firewall can handle at a given time. Because a firewall acts as a gateway between your internal LAN (local area network) and the external public-facing Internet, the appliance must track and map the IPs (internet protocols) of all original internal requests and the external IPs assigned to them when requests are sent across the web. The Maximum Connections stat indicates how many internal and external mapped IPs can be simultaneously tracked by the security processor. This stat is important when choosing a firewall particularly for companies with employees who use several applications at once. The FortiGate-60F supports up to 700,000 concurrent TCP connections.
Other things to consider
There are a ton of other factors that can determine which appliance is the best fit for your needs. The specific form factor of your appliance–its physical size and shape–may be an important determination if you’re deploying in a small office where space is a limited commodity. Depending on the complexity of your network setup, the amount and types of interfaces (ports) can impact how you connect routers, network switches, high availability firewalls, and other auxiliary security devices. Knowing what kinds of swappable components or add-on modules are available can be important for businesses that must customize appliances to fit a tricky deployment where temperatures, memory requirements, or availability of power supply are an issue. It is also important to note the maximum site-to-site VPN or IPSec tunnels a firewall can support if your business plans on employing a large number of remote workers.
Arming yourself with a brand-specific Buyer’s Guide can simplify the process of choosing the right firewall. Educating yourself through blogs, podcasts, or video reviews can also remove a lot of stress from the decision-making process. However, the best way to ensure that the firewall you purchase is a perfect match is to speak with a knowledgeable, certified representative. You can reach one at Firewalls.com by calling 866-403-5305. Not ready to hop on the phone to discuss your needs? Connect via live chat or email sales@firewalls.com to find your perfect network security solution.





