Here at Firewalls.com, we love hearing from you. Just last week, we got a great topic suggestion for a blog post from a reader: an affordable firewall for remote employees that seamlessly interacts with headquarters.
So without further ado, here’s one way you might go about addressing this increasingly common scenario. Check out our first entry in a series we’re calling, “You Asked, We Answered.”








Firewalls for Remote Employees: A SonicWall Setup
Let’s tick off the boxes of the request. First of all, we need to identify a firewall model ideal for fairly heavy use in a remote setting. How about the SonicWall TZ270. One of the newest of SonicWall’s Gen 7 firewalls can handle a power user with multiple devices and still run even the most complex security services.
What are those services? With the Total Secure Advanced Edition bundle, the TZ270 runs:
- Gateway Anti-Virus, Intrusion Prevention, Application Control
- Content Filtering Service
- 24×7 Support
- Network Visibility
- Basic DNS Security
- Anti-Spam
- Capture ATP (Multi-Engine) Sandboxing
- RTDMI Technology
- Cloud Management
- 7 Days Cloud-based Reporting
That’s a pretty lengthy and advanced list that’ll protect your network at home (and thereby at HQ) from the most advanced threats, from email to web-based hazards and everything in between. Around the clock support means even if your remote workers keep a non-traditional schedule, they’ll be able to get in touch with an expert whenever they need to. And those last two bullets may be the biggest key when it comes to communicating with headquarters, but we’ll get to that in a second.
By the Numbers
Before we get to that, let’s not forget performance. The TZ270 has a firewall throughput of 2.0 Gbps, that’s a lot of speed in a small package. Even with just about all those aforementioned services running, the Threat Protection Throughput clocks in at 750 Mbps, supporting connection speeds that exceed what just about any home users have. It also comes with 5 IPSec VPN clients (supporting up to 200) and 1 SSL VPN client (supporting up to 50) for that very necessary secure remote access.
On the hardware side, the TZ270 offers 8 GbE RJ45 ports, plenty to connect a robust home network, and 2 USB 3.0 ports to connect 3G, 4G, and yes, even 5G & LTE modems. And we mentioned small package – this is a compact device that easily tucks onto a desktop, bookshelf, table, or whatever your remote employees may use. The wireless model, the TZ270W, also acts as an access point with the same footprint aside from a couple external antennas.
Connecting with HQ
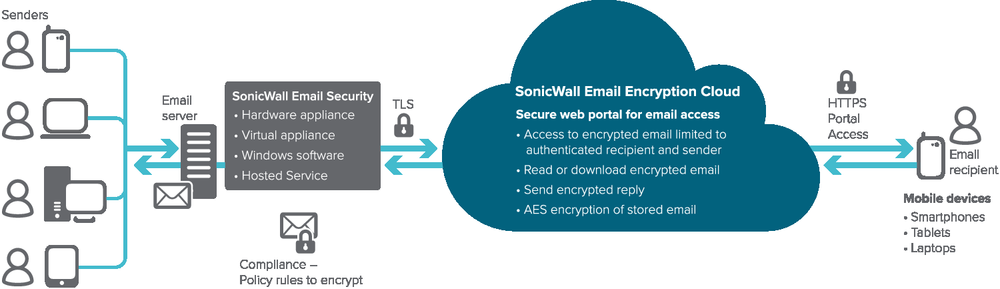
Back to the other part of the question, connecting your remote workers to the mothership. Whether your main office SonicWall firewall is small or large, remote deployment and management is a breeze. Let’s start with deployment. You won’t need to send IT staff to each remote household to set these TZ270s up. With the SonicExpress app, you can deploy one or several new firewalls with your desired settings remotely.
On top of that, the firewall features auto-provision VPNs, so no on-site configuration necessary there either. Once they’re up and running, your IT pros can manage as many firewalls as your organization has at once. That’s thanks to Network Security Manager 2.0, which offers single-pane-of-glass management, analytics, and reporting with an improved user experience. NSM works for single and multiple firewall scenarios. That means not only can you monitor everything from one place, you can make configuration tweaks that way, too.








Affordability
We can’t forget this last part of the question. As they say money talks and something (I forget what) walks. An appliance only TZ270 retails at $465, with the TZ270W MSRP a hundred bucks more. As we mentioned before, you’ll want services to maximize your firewalls. The recommended 1-year TotalSecure Advanced hardware bundle (including both appliance and advanced service suite) retails at $865.
But a big disclaimer here, if you reach out to a Firewalls.com expert via phone or online chat, you will get a better deal. On top of that, they can walk you through any questions you may have about a remote work setup for your staff. Give them a call at 866-957-2975 or simply pop open the chat window on our site and start typing to get started today.