This Sophos vs Fortinet comparison lets you size up the XGS 4500 and FG-400F, while focusing on the unique specifications and security features involved.


This Sophos vs Fortinet comparison lets you size up the XGS 4500 and FG-400F, while focusing on the unique specifications and security features involved.

Managed network monitoring delivers proactive security, 24/7 protection, and scalable oversight without the cost of in-house IT staff.

Explore the top rated data center firewalls for modern enterprise security, including options from SonicWall, Fortinet, and Cisco Meraki.

Explore how an IT risk management policy combined with AI-driven security enhances threat detection, compliance, and overall cybersecurity.

Learn about how to prevent data breaches in healthcare and the overlap in security demands and risks with telehealth platforms.

Building network infrastructure with cyber insurance eligibility in mind helps reduce risk and improve insurability for the long term.
Learn how IT infrastructure best practices support secure, efficient mergers, acquisitions, and consolidations.
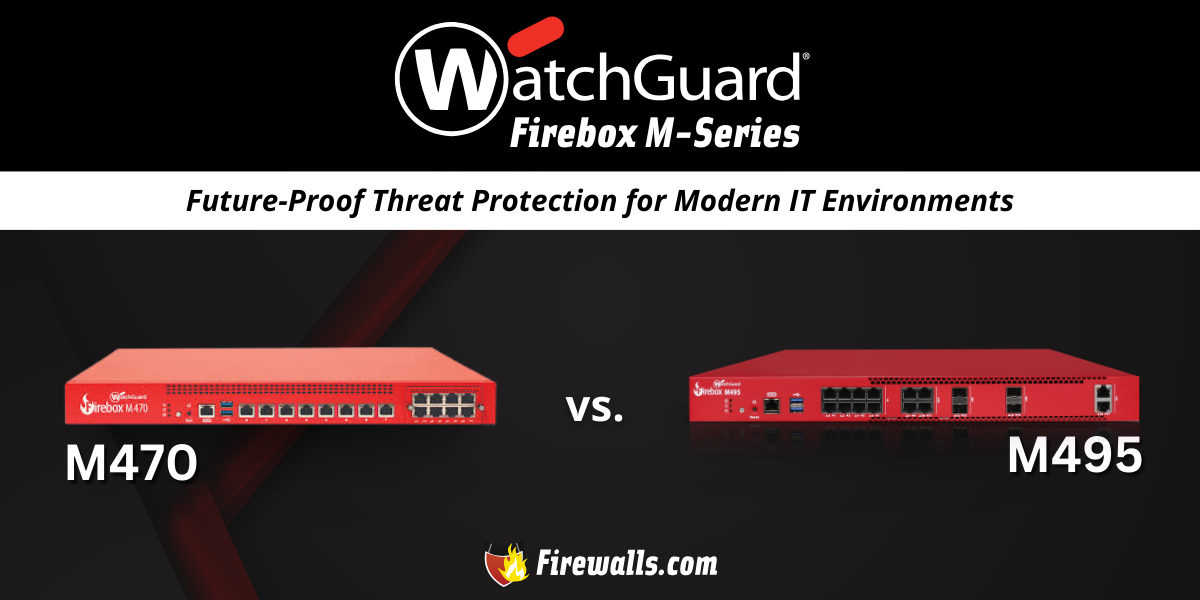
Take a closer look at this firewall comparison between WatchGuard Firebox M470 vs M495 to determine which specs differ the most.

Learn about important FinTech app security solutions and how next-gen firewalls and future-proof strategies keep financial data secure.
Compare SonicWall vs Fortinet firewalls to find the best security solution for your business, exploring features and deployment options.